Over the last two weeks there’s been a huge focus on spying, privacy, and data security. In the wake of Edward Snowden’s leak of details about the NSA’s worldwide surveillance program, PRISM, we wouldn’t blame every web user for thinking that somebody’s looking over their virtual shoulder.
First thing’s first, though. Nobody’s out to get you. With an incredible amount of data passing through the internet each day, government agencies would need a lot of manpower (and processing power) to sift through it all. Cat photos aren’t threatening. And mentioning “President Obama” and “bomb” in the same email might get you on a watch list for a few seconds, before real threats take priority. Given the secrecy of the programs and institutions involved, it’s impossible to know how much of your information is being intercepted – even though it is being discarded – and it’s also difficult to make absolutely 100% sure that you have impenetrable communications. If the scary government men want something, they’ll get it. It might also serve you well to not be too paranoid: encrypting all of your emails, web sessions, and voice calls will make you look suspicious, after all. But really, you’re the average user is no more at risk of having their emails snooped now than they were 6 years ago. The real issue is just that it’s possible, now.
If you’re still convinced that men in black are reading your emails, we have 5 tips for getting yourself off those virtual watch lists. Or at least further away from them – after all, there are no guarantees that they aren’t out to get you.
1) Safe and sound at home
Have you been browsing some dodgy websites? Has that black van been parked on your street for the past three days? Well, how about you get the basics down and just secure your home network. Believe it or not, sniffing wireless packets is incredibly easy and can be done with software that’s freely available on the internet. What you want to do is make sure your wireless network has some form of security.
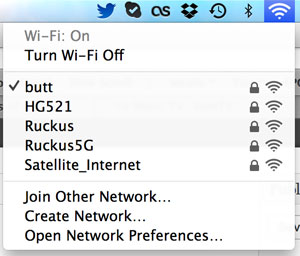
If you already require a password to access your wireless network, you’re one step closer to being more secure. If you’re uncertain, use the network tools in your operating system to find out. On Windows 8 you can click on the wireless icon in the system tray and it brings up the list of networks. Hover your mouse over the network you are connected to and it’ll show security information.

Mac users, you can simply click on the wireless icon in the menu bar. Any network that requires a password will have a lock icon next to it.
If your wireless network does not have a password you’ll want to enable that. Check with the manufacturer of your router to get instructions for enabling wireless security.
2) Get on a secure channel
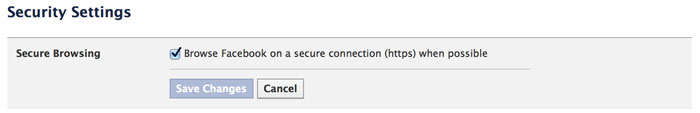
Communications traditionally run between your computer and the server it’s communicating with. In between, though, data can be intercepted. This is where you want everything to be encrypted, because whoever intercepts your data can do nothing with it if it’s encrypted (well, they’d need a lot of time on a supercomputer to decrypt it). For this, you’ll want to make sure that websites you’re using use SSL (secure sockets layer). Twitter has it enabled by default, Facebook lets you enable it manually.
This means that a secure tunnel is established between your computer and the website: anybody listening in will only get encrypted signals. If you’re uploading content to a server via FTP, speak to your web host about enabling SFTP (S for secure, y’see). At the very least it means your data is safe from any intermediary intercepts.
If you want to remain anonymous, rather than protecting your private data, you can use a service like Tor. This will route your requests across servers, worldwide. However, Tor endpoints (where your data leaves the Tor network) can still be monitored for decrypted data. It’s most useful for keeping a low profile, but your data can still be monitored.
3) Scan, scan, scan
Malware is one of the most popular means for data to be harvested. While most malware is written by syndicates that want your personal information and credit card numbers, it’s not beyond government agencies to do the same. In fact, part of the current scandal involves G20 attendees having their data and keystrokes intercepted by malware monitoring software installed on computers at internet cafes.
Install a decent anti-virus and malware scanner on your computer to make sure you’ve not got any malicious software designed to harvest your information.
4) Ditch that snitch
If all else fails you can simply cut out the companies implicated in PRISM. Google, Facebook, and Apple have all said that the NSA doesn’t have wholesale access to their systems and data is only provided when requests are submitted through the proper channels. If you don’t feel comfortable with the possibility that your emails or Facebook messages are going to be read by government agents, simply stop using those services. The nine companies listed as participating with PRISM are: Facebook, Google, Apple, Yahoo, Microsoft (Hotmail), PalTalk, AOL, Skype, and YouTube. You can cancel your accounts with those services, but there’s no guarantee that closing your account means the data is gone.
While Facebook will be difficult to replace, you can find replacement providers for the services offered by the others. Skype’s VOIP call functionality can be handled by Viber. Google, Yahoo, and Microsoft mail can be handled by many of the other free email providers – just choose a provider that offers encryption. And web search functionality is handled by DuckDuckGo – admittedly not as good as Google, but sacrifices will have to be made for the promise of privacy.
5) Trust nobody
Like agent Mulder, you’ll have to make peace with the fact that nothing is beyond the reach of governments and secret service agencies. Voice calls can be intercepted (South Africa even has a law for it – remember RICA?). Electronic communications, thanks to the prevalence of the internet, are just that much easier to monitor. Best practices would be to keep as much of your data offline as possible. Don’t rely on services that need user accounts, because these are used to mine usage patterns and any information you store. Convenience is often used to mask something that ends up being a means for companies to gather data.
If you must connect, do so anonymously. Public Wi-Fi hotspots can be hit and miss: there’s no telling whether the company running the access point is selling your data, or monitoring it.
If you absolutely must store things online, use services like SpiderOak. This Dropbox-like internet file store uses an irretrievable password to encrypt your data. Lose the password, and you lose access to your content. Bad news for you, but even worse news for those snoopy spooks that simply must know everything.

