Next Tuesday, 11th February, is the #TheDayWeFightBack against mass surveillance and gross invasions of privacy online. In the run up to the event, we’ll be publishing a series of posts on the subject of protecting your data online and how big the problem of warrantless surveillance is in South Africa. Our regular columnist and legal eagle Paul Jacobson is going to start us off gently, with some tips on keeping yourself to yourself.
Unless you have been living on a remote hill with no technological connection to the world, privacy is no longer about secrecy, it is more about whether you can control how your data is used and by whom? Lately it seems that our ability to control our data may largely be an illusion and it is tempting to stick your fingers in your ears and stop listening to the news.
Before you do that, take a look at these 5 ways you can better secure your data.
Step 1 – more secure file transfers
Many of you use Dropbox for file sharing. Dropbox is pretty secure. It transmits your data to its servers (well, Amazon’s servers which Dropbox operates on top of) using fairly decent encryption and encrypts data it stores on those servers. The challenge with Dropbox is that you don’t control the decryption keys for your data. Dropbox does, and you won’t necessarily know if or when Dropbox decrypts your data in response to a demand by law enforcement authorities.
If you just need a way to securely move data between trusted devices, consider BitTorrent Sync which was developed by the same people who came up with the technology that powers your other (legitimate) file sharing activities. BitTorrent Sync differs from Dropbox in that Sync is a peer-to-peer file sharing tool where data is transferred directly to approved devices and not through an middle man or server.
Sync has some limitations: you’re devices need to be online to share from one to another (no cloud server unless you configure one yourself) and Sync doesn’t have a way to revoke access you have granted to someone else and remotely remove your data. On the plus side, Sync is pretty secure and you can install Sync apps on Android and iOS devices for easy file sharing between mobile and desktop.
Step 2 – more secure email
How secure is your email? Do you know if your provider uses decent encryption to protect your data from being intercepted? Not all providers do. If you use Gmail you are already using a relatively secure email service. Google has made secure connections the default and also protects connections between its servers (and has said it will strengthen these links even further in light of recent NSA interception revelations). Other email services are stepping up with better security too so make sure you know how well they protect you.
You may prefer not to trust your email with Google, Yahoo, Microsoft or any other cloud service (at least not entirely). You can start securing your desktop email app with freely available software based on Pretty Good Privacy (“PGP”) tools. GnuPG is a “complete and free implementation of the OpenPGP” protocol and offers software for Windows, Mac and (probably) Linux. You’ll need to configure the software yourself but you should be able to create encryption key-pairs to encrypt your emails and self-sign them. Encrypted mail is a terrific idea but that is only viable if your recipients are also using similar encryption tools.
Step 3 – More secure Twitter
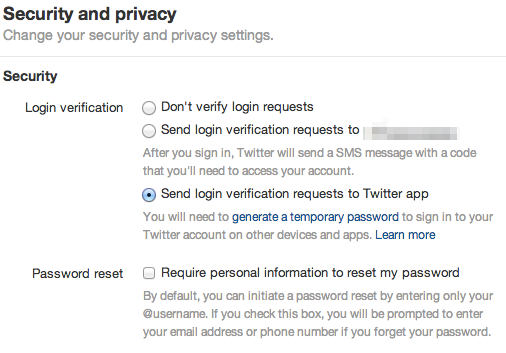
Twitter is actually pretty good with encryption and data protection and not many people realise just how forward thinking Twitter is. Twitter has set encryptions to its services to more secure connections by default (look for “https://” in your browser toolbar). If you use the Twitter apps on your mobile devices, you can add an additional layer of security that is just amazing.
If you enable the option to send login requests to your Twitter app (if you have the Twitter app installed on your tablet and phone, pick one) then you will be able to approve login attempts using your device before the login will succeed. Simple and yet the technology behind this is awesome (terrific discussion on Security Now 416).
Step 4 – More secure Facebook
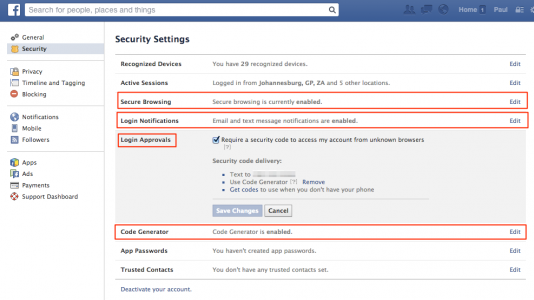
Despite all the ways Facebook collects your data and uses it, there are a quite a few ways you can better secure your account. Visit your security settings and spend some time enabling and configuring these options:
Enabling secure browsing and the Code Generator in your mobile Facebook app are pretty important starting points because they go a long way towards preventing people from intercepting your Facebook use and from hacking your account.
Step 5 – More secure Google
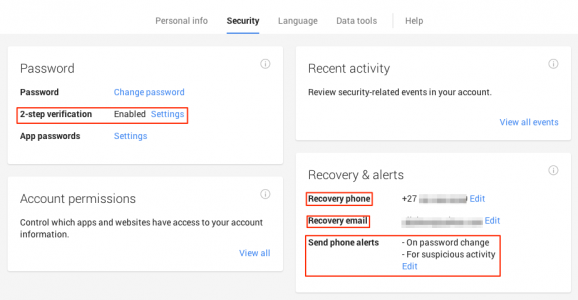
Your Google account settings affect much of what you do on Google. As with Facebook and Twitter, you really should enable “2-step verification” for your Google account. You can use Google’s Authenticator app (iOS and Android) or other authentication apps like Authy to generate random codes to better secure your account. That protects your account (including Gmail) from some unauthorised person impersonating you because it uses your mobile device to authenticate you to Google (so don’t lose them).
Make sure you set up a recovery phone number (Google supports SA mobile numbers) and email address because that is how you should be able to regain control of your account if it is hacked. Google can also send you SMS notifications of any password changes and suspicious activity so enable all of these options.
Now that you have done all of this, stick your fingers in your ears and go have a nap.