Remember when, a couple of years ago, hacker group Lulzsec used to talk about it’s ‘LulzCannon’ technique for launching massive Distributed Denial of Service (DDOS) attacks on unsuspecting websites? The Chinese government apparently has a tool for launching DDOS that makes the LulzCannon seem like the internet equivalent of peashooter.
A team of researchers from the universities of Toronto, California, Berkeley and Princeton have just published a report on Citizenlab which outlines a “Great Cannon” operated by the Chinese government. It’s based on DDOS – a type of attack where multiple computers (thousands or millions) all attempt to access a website simultaneously – but on a grand scale. The researchers claim that the Great Cannon is related to the infamous Great Firewall, through which the government tracks all data going in and out of the country and blocks access to international sites it doesn’t like – but is a separate piece of technology designed for attack.
Their research was conducted by analysing a recent attack which took down coders’ collaboration website Github.org last month. The attack was sophisticated, and so hard to block that it took over 100 hours to fight off. Initially analysis fingered Chinese ecommerce site Baidu as the culprit, suggesting that its servers had injected malicious code into visitors’ browsers that unknowingly turned their computers into part of the attack.
After 113 hours of sustained DDoS attacks our defenses are holding. We will keep our status at yellow until the threat has subsided.
— GitHub Status (@githubstatus) March 30, 2015
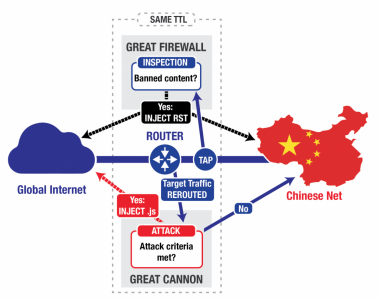
The Citizenlab team, however, say that Baidu was probably innocent, and the origins of the attack were something new. Servers related to the Great Firewall network intercepted traffic going to and from Baidu, and injected attack code while data was in transit.
“In the attack on GitHub and GreatFire.org,” the authors write, “The Great Cannon (GC) intercepted traffic sent to Baidu infrastructure servers that host commonly used analytics, social, or advertising scripts. If the GC saw a request for certain Javascript files on one of these servers, it appeared to probabilistically take one of two actions: it either passed the request onto Baidu’s servers unmolested (roughly 98.25% of the time), or it dropped the request before it reached Baidu and instead sent a malicious script back to the requesting user (roughly 1.75% of the time). In this case, the requesting user is an individual outside China browsing a website making use of a Baidu infrastructure server (eg. a website with ads served by Baidu’s ad network). The malicious script enlisted the requesting user as an unwitting participant in the DDoS attack against GreatFire.org and GitHub.”
They illustrate the attack process in the graphic below.
According to the report, visitors to Chinese sites could protect themselves by forcing their browser to use HTTPS encryption, but as that’s not supported by many Chinese sites it may not be an option.
The researchers explicitly point to the Chinese government as the originators of these attacks, and discuss the policy implications. What is surprising, they say, is that the government used the Great Cannon brazenly enough to draw attention to itself, and that it seems willing to jeopardise the reputation of one of the country’s largest internet organisations.
“The incorporation of Baidu in this attack suggests that the Chinese authorities are willing to pursue domestic stability and security aims at the expense of other goals, including fostering economic growth in the tech sector. Selecting Baidu’s international traffic may appear counterproductive given the importance of Baidu to the Chinese economy: the company enjoys stature as one of China’s ‘big three’ Internet firms, alongside Alibaba and Tencent, and currently ranks as the top site in China.”
It’s worth noting that the largest single shareholder in Tencent, which makes the WeChat messaging app, is South African media firm Naspers, whose share price has just risen above R2 000 for the first time largely based on its investment in Tencent.
[Image – CC Methodshop]