There is a horrible misconception that iOS devices and apps are virtually immune to any kind of malware attack, but that couldn’t by further from the truth.
The vulnerabilities in iOS apps were once again highlighted in a recent security update, discovered by Minded Security Research Labs, in which some strange behaviour was noted in apps that use the AFNetworking library.
“It turned out that because of a logic flaw in the latest version of the library, SSL MiTM – “man in the middle” – attacks are feasible in apps using AFNetworking 2.5.2,” Minded Security Research Labs wrote in a blog post.
In the security company’s initial finding it revealed that over 100 000 iOS apps out of the 1.4 million total are vulnerable – and a lot of them are South African apps that are used by thousands of people every day, including online banking customers.
“AFNetworking recently had a major security flaw. Due to lack of SSL cert validation, the proverbial coffee shop attacker could easily bypass SSL and see all your app’s user credentials and banking data,” SourceDNA explains, who is in the business of analysing the security of cellphones, game consoles, and microcontroller firmware.
What does this mean to people making use of vulnerable apps over a public network? Well, SourceDNA explains that “this meant that a coffee shop attacker could still eavesdrop on private data or grab control of any SSL session between the app and the Internet. Because the domain name wasn’t checked, all they needed was a valid SSL certificate for any web server, something you can buy for $50”.
SourceDNA developed a website which iOS users can use to check which developers have created apps that are vulnerable to the SSL MiTM attacks.
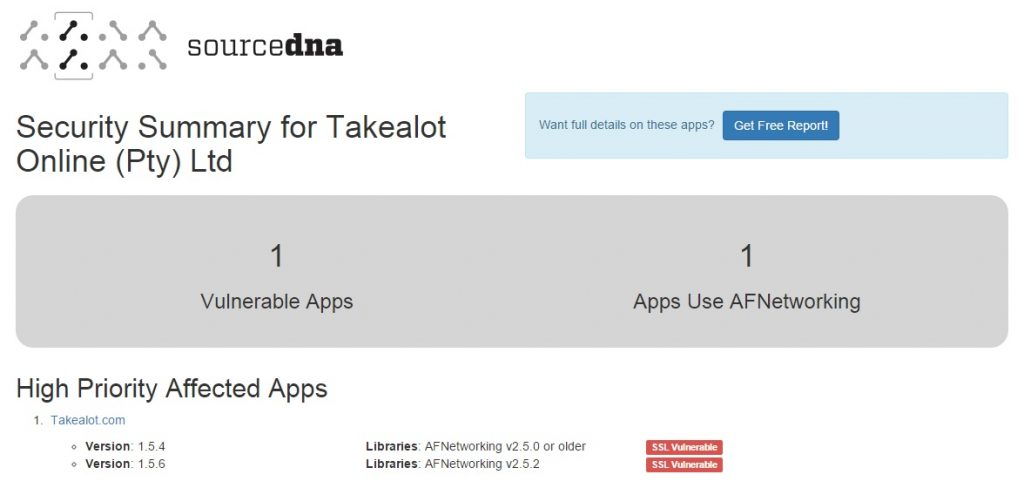
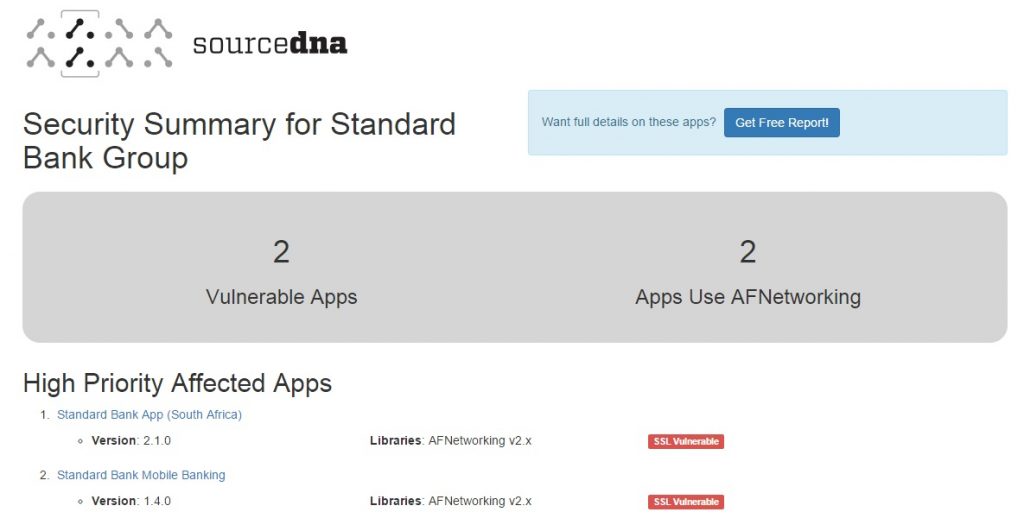
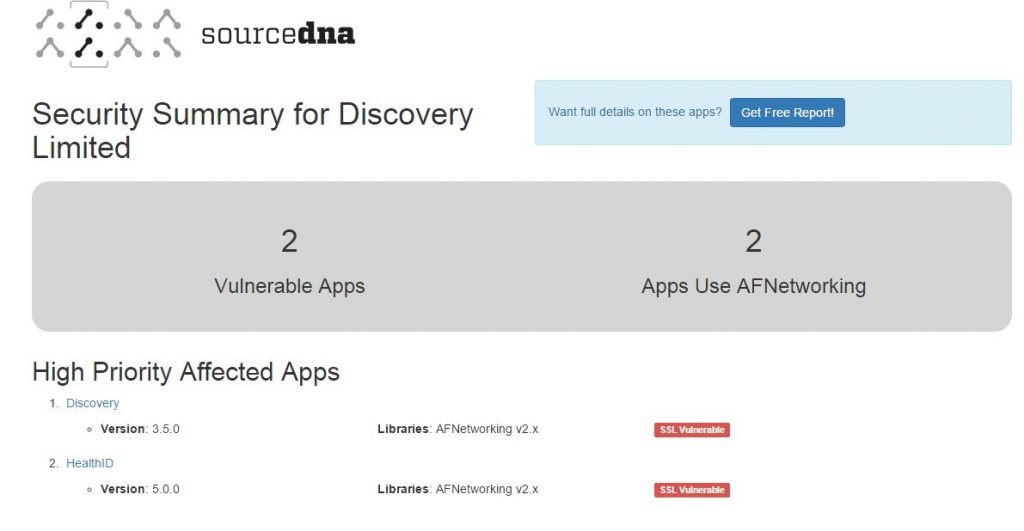
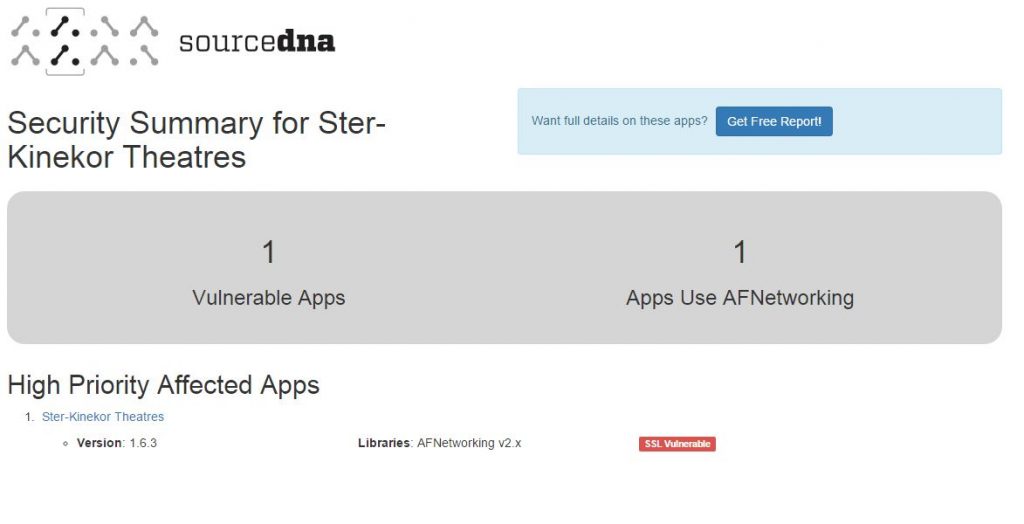
Eagle-eyed reader and Chief Technology Officer for BidorBuy, Gerd Naschenweng, discovered by using the checking website from SourceDNA that some of South Africa’s most-used apps are vulnerable to attack, which he pointed out in his blog.
Some of the vulnerable apps are:
Takealot
Standard Bank
Discovery
Ster-Kinekor
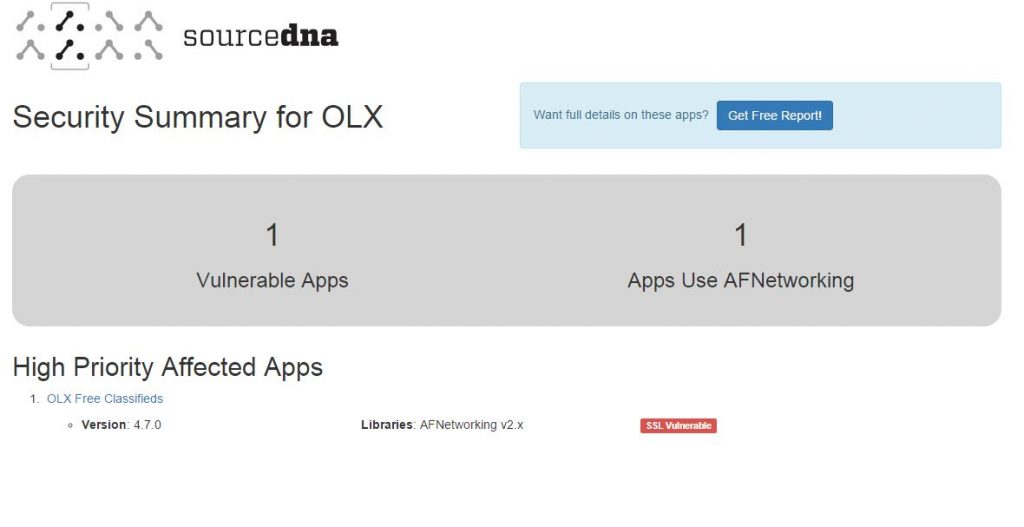
OLX
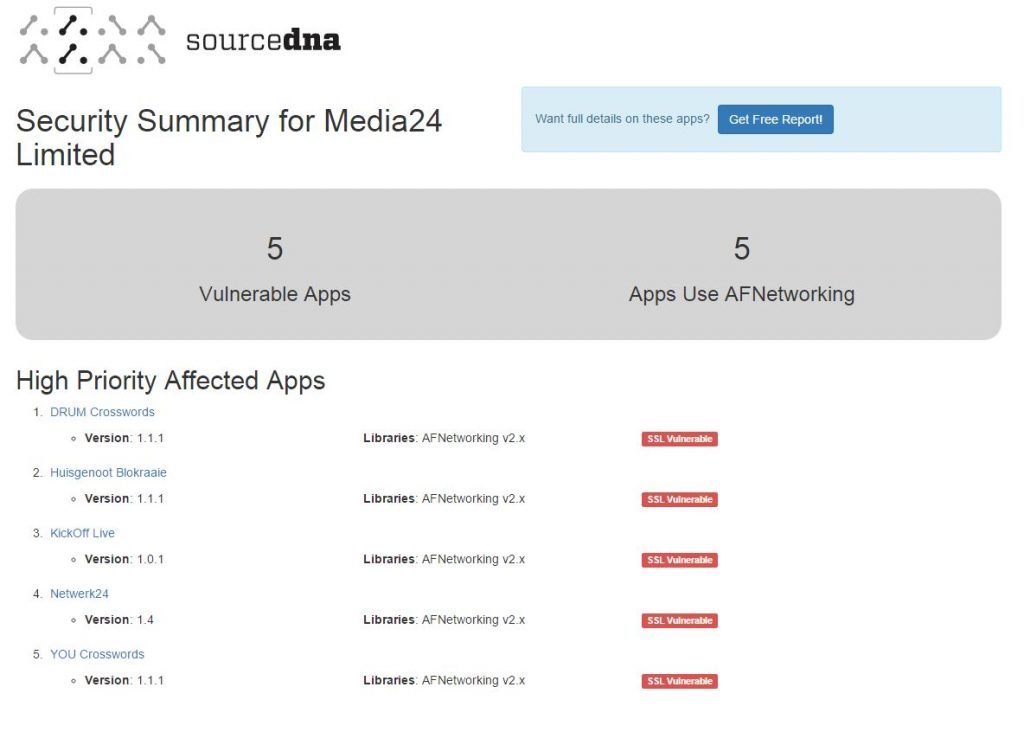
Media24
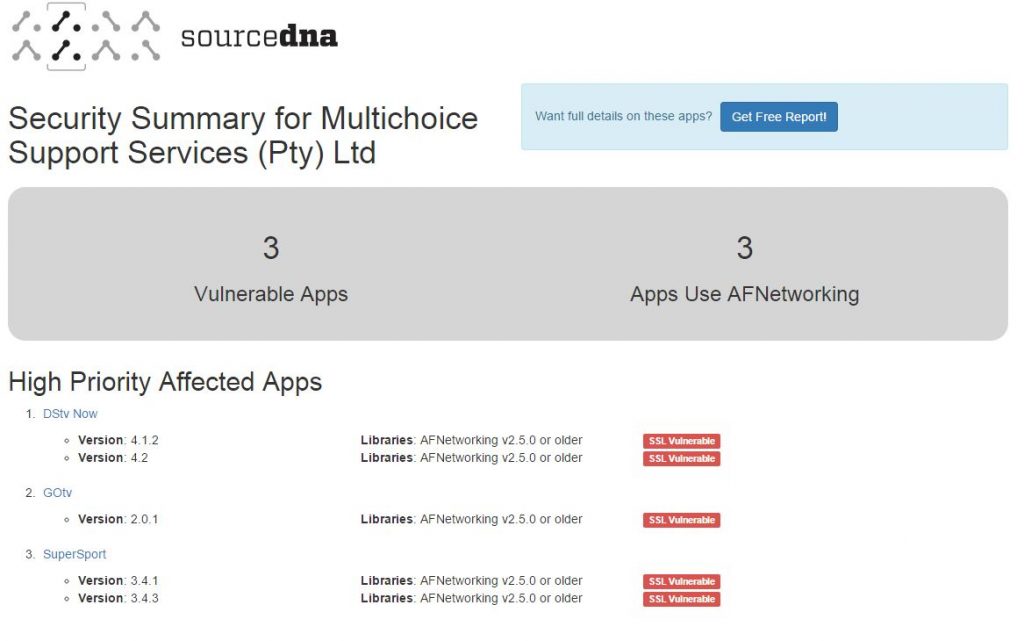
Multichoice/Supersport
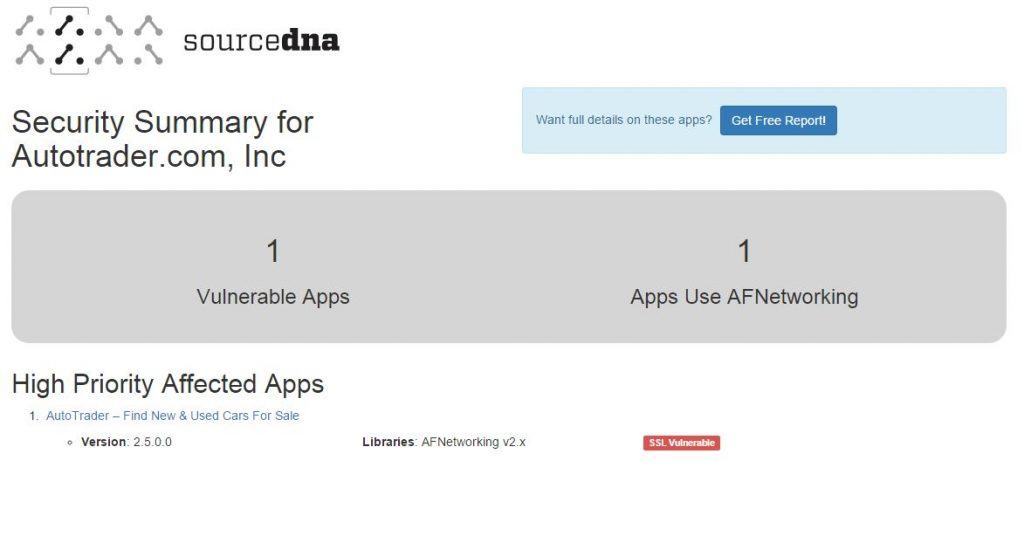
Autotrader
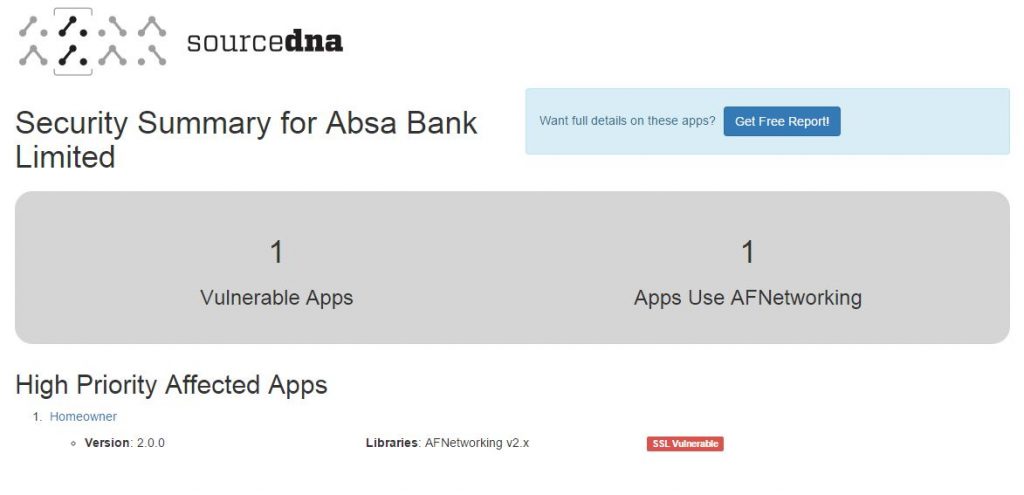
Absa
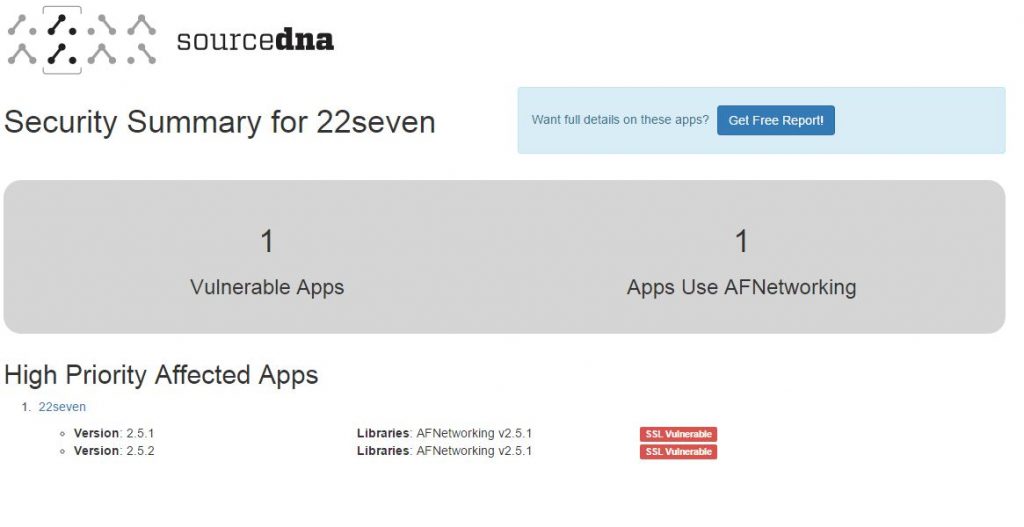
22Seven
The chances of an MiTM attack successfully breaching the walls of your iOS phone is pretty low if you are on a secure network at home or in the office. But if you make use of public WiFi facilities such as those in airports or malls, it will leave you wide open to man-in-the-middle attacks.
To remedy the vulnerabilities in the apps affected, the various app developers have to update their creations and plug the holes. On your side of things, if you are concerned about being a possible victim, refrain from using these apps altogether.
Remember, you can always check which of your apps are vulnerable to attack by clicking here.
Absa has reached out to us, stating that its Homeowner app is not vulnerable, according to its internal testing.
“In the normal course of business, Absa regularly conducts thorough technical tests on all of its applications, including the Absa Homeowner App. We can confirm that this application has not been impacted by AFNetworking issues. The Absa Homeowner App uses a version which is not impacted by the vulnerabilities reported in v2.5.1 and v2.5.2 and therefore no changes are required,” it said in a statement.
[image – Shutterstock]