If for whatever reason you haven’t updated your iPhone or iPad to iOS 9.3.5 you might want to do so immediately.
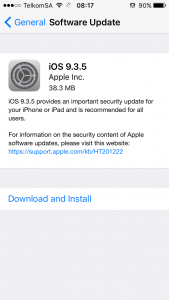
The reason for this urgency is that the update patches multiple zero-day vulnerabilities which, if exploited can allow an attacker to remotely jailbreak an iPhone 6 and give an attacker full access to a handset. So before you read further, top what you’re doing right now head to Settings > General > Software Update and start downloading.
The vulnerability was discovered when human rights defender, Ahmed Mansoor received a suspicious text message which contained a link, and a promise to reveal secrets about how detainees in United Arab Emirates prisons are tortured. Mansoor forwarded the message along to Citizen Lab researchers who identified the link as an exploit infrastructure linked to NSO Group.
NSO Group, according to Citizen Lab, is a “cyber war” company which flogs a lawful intercept product called Pegasus. This software is exclusively available to governments at a cost of $8 million for 300 licenses.
Had Mansoor clicked the link in that text message, spyware would have seized his phone and given an attacker the ability to listen in on his surroundings, access the camera, record his conversations, track his location and even log his chat messages.
After discovering the vulnerabilities, Citizen Lab notified Apple who promptly responded by pushing out update 9.3.5 yesterday.
How it works
The link in the text message is to a webpage which loads JavaScript and grabs remote binary files. This is made possible by a vulnerability in the WebKit rendering component of the Safari browser which allows the binary files to be executed.
From there, the binaries bypass Apple’s protection for its operating system known as Kernel Address Space Layout Randomization (sic), which usually prevents malware like this from finding the where the core of the system is located.
Once the executable knows where to plant its malicious seed, a third exploit triggers which effectively disables iOS from blocking software not signed by Apple.
After this sequence of events has completed will the spyware be loaded which also disables automatic updates, removes any other jailbreaks and persists through a reboot.
The risk
This exploit is currently linked to a group that sells spyware to governments who want to take action against critics such as Mansoor. This means that unless you’re a member of a vocal civil society group in an oppressive government you might not be a target, yet.
The revelation of these vulnerabilities is particularly dangerous for the folks that don’t keep their software up-to-date because it could mean that other malicious individuals are able to exploit unpatched systems.
For this reason we recommend updating your iPad or iPhone immediately, just to be safe.
[Source – Citizen Lab]

