Everything from your security system to your kettle is being connected to the internet, and that is, in many ways a good thing: feature-packed, remote controlled devices talking to each other can make your world a little bit more convenient and intelligent.
But how aware are you about the bad side of the so-called “internet of things”? The first major detected global malware attack on internet connected devices occurred recently, and it shows how precariously we’re living and how little thought is being given to securing the internet of things.
The malware in question is known as Mirai (not to be confused with a car of the same name) and its source code was published on the internet for ne’er-do-wells to use earlier this month. The point of Mirai is simple: find and break into connected devices and co-opt them into a botnet that can be used for bad things, like distributed denial of service (DDOS) attacks.
Mirai hit the headlines recently because it was used in a well-publicised attack on the highly regarded website Krebs on Security. At its peak, malicious traffic was flooding to the site at a rate of 620Gbps.
Thorough analysis of attacks perpetrated by Mirai by Incapsula and MalwareTech have suggested that the malware has a favourite type of device to install itself on. A device whose use has increased at a prolific rate in recent years yet is often overlooked when it comes to security. The internet-connected video cameras.
According to the researchers, Mirai scans for these kinds of devices (it’s not just video cameras) and then begins a a dictionary attack method to “guess” username and password combinations. It’s been astonishingly successful – there are hundreds of thousands of connected devices like routers and cameras infected by Mirai, and new vulnerabilities are being discovered at a regular pace.
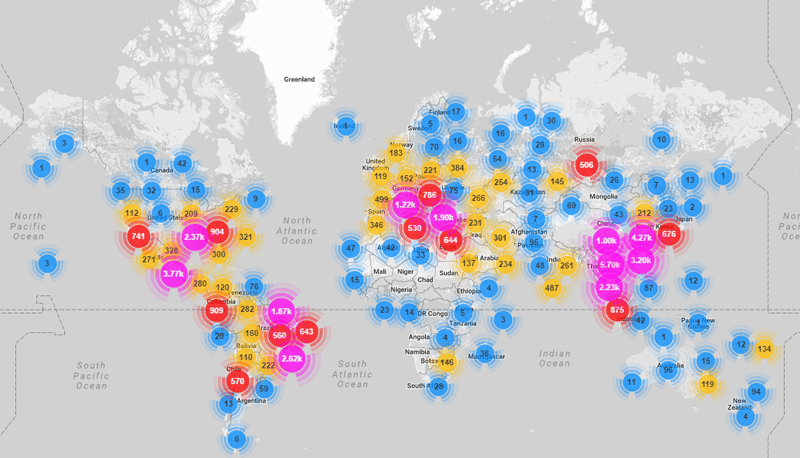
The video below was created by MalwareTech and shows how Mirai has spread so far.
We were curious to see just how vulnerable South Africa’s internet of things is to a Mirai infection.The good news is that in the map published by Imperva showing detected nodes, there are just over two dozen devices definitely in the wild (although our northern neighbours don’t get off so lightly).
But is that because South Africans are particularly security conscious? Probably not.”Not a lot of devices are connected to the internet [in South Africa],” says Andre Baumann of CCTV distributor Reditron.
We contacted Baumann because his firm imports cameras made by the Chinese manufacturer Dahua. In that map above, Dahua’s devices and devices running Dahua firmware crop up very regularly as being infected. That doesn’t mean other brands are necessarily safer, of course.
What should have been shocking – but frankly wasn’t – was that the resellers of Dahau gear we spoke to weren’t aware of the Krebs’ story or of Mirai, and they didn’t know of any plans to patch cameras to prevent future infection.
And Mirai is just one of many known and – probably – unknown pieces of malware targetting the internet of things. Most of the risk can be mitigated, Baumann says, by corporate clients who create a standalone network just for CCTV cameras.
“When a device is connected to the internet we do try to provide it with static IP addresses and connect it to a VPN, depending on the client,” says Baumann.
The trouble is that in the consumer and non-tech business world, we want our cameras connected to the public internet, so we can see the dogs at home or monitor our gate security from afar. Unless you’re using a VPN to connect to your remote cameras, the only thing that stand between them and Mirai-like infection is a password.
With that having been said, if Mirai manages to guess the password, the network is open to attack.
We asked John Eigelaar of Keystone Electronic Solutions, a Centurion-based engineering firm which has just begun selling security camera systems, about the video-powered botnet. Eigelaar says that camera manufacturers have made life harder for those trying to protect them from attack.
“I’m not surprised,” Eigelaar says, “The problem with cameras is that everyone wants to lock you into a system. None of the source code is available and many of the features advertised on the box simply don’t work.”
Vendors, Eigelaar says, often try to ensure that their cameras are only fully functional with their DVR recorders and gateway devices. So proprietary firmwares are the order of the day, which creates a security issue as it restricts the ability of resellers to ensure they’re not a threat to other systems.
For commercial deployments, Eigelaar also says his customers either keep networked cameras off of the public internet, or link them using secured VPNs.
The secret intruder
The trouble with Mirai is how wily it is. At time of writing there is no way to avoid being targeted and simply resetting the device and purging the volatile memory Mirai infects is a temporary solution.
Suggestions for preventing an infection according to Incapsula include not using default or generic usernames and passwords as well as disabling all remote access to the devices. To find out which remote access ports are currently open Incapsula recommends using this tool to scan ports 20 (SSH), 23 (Telnet) 80 (HTTP) and 443 (HTTPS) on devices by plugging in the relevant IP addresses.
MalwareTech reports that once Mirai infects a device it locks down these ports to prevent remote access by the owner and other malware.
Another solution is for manufacturers of cameras to push out firmware updates. Baumann says that a security camera can be patched but it needs to come from the manufacturer. “Security patches can be distributed by the resellers and would be checked against the manufacturers API and installed. The patch itself would have to be created by the manufacturer,” concludes Baumann.
“It’s definitely time that manufactures stopped shipping devices with global default passwords and switch to randomly generated passwords displayed on the bottom of the device,” says MalwareTech.
Mirai’s existence has brought into sharp relief the need for a discussion about the security of the internet of things. “Smart” devices are becoming ubiquitous in our cities. We’d be stupid not to take notice of them.
[Image – CC BY 2.0 rafael parr]

