Wikileaks has published 8 761 documents and files from the CIA’s Centre for Cyber Intelligence that showcase the agency’s hacking capabilities.
This data dump is the first that Wikileaks says it will publish and it’s titled it Year Zero. The entire collection of documents is called Vault 7 and so far it reads like a cyber security professional’s worst nightmare.
The documents show just how proficient the CIA is at taking control of devices whether it be and Apple iPhone, an Android phone or a Samsung Smart TV.
In the case of Smart TVs, Wikileaks revealed a project called Weeping Angel. This hack was developed in tandem with MI5 in the UK and would allow the CIA to listen to your conversations via your TV. It is alleged that the CIA could use a “fake-off” mode, which would allow the CIA to power the TV on without the owner knowing it.
“In ‘Fake-Off’ mode the TV operates as a bug, recording conversations in the room and sending them over the Internet to a covert CIA server,” said Wikileaks.
Encryption is a hurdle easily vaulted
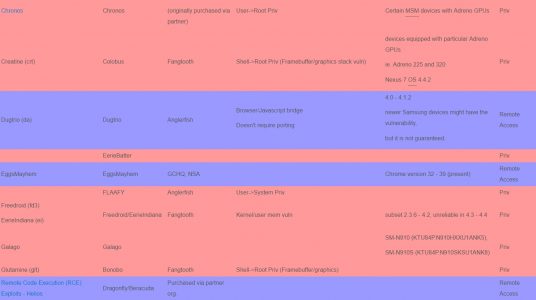
Wikileaks has also detailed a number of exploits that can be used to infect a smartphone. The document dump details a number of zero-day exploits for both Android and iOS devices which could be used along with malware to control and extract data from a smart device.
Having malware on a phone means that the CIA wouldn’t need to worry about decrypting your WhatsApp chats because it can glean the data before encryption is even applied.
More worrying is the claim that the agency hoarded zero-day exploits. The biggest problem with this is that zero-day exploits can be found by anybody with enough time and who’s to say that those folks will be responsible with that information and inform the firms that need to be informed?
The CIA certainly didn’t.
Wikileaks says that the CIA made all off these tools unclassified. Simply put, if you were a nefarious individual working for the CIA – or a hacker that had breached the network – and you got wind of these tools they could be used with little recourse.
“The CIA has primarily had to rely on obfuscation to protect its malware secrets,” explained Wikileaks.
This first slew of documents covers 2016 but Wikileaks says Vault 7’s breadth extends as far back as 2013 and that it will release more documents obtained from its anonymous source at a later stage.
We now wait with baited breath for Donald Trump’s first tweet about all of this…

