Security researchers at Mimecast have discovered a potential flaw in email that, if exploited by cybercriminals, has the potential to defeat all but the most robust IT security systems and sophisticated users.
At least, that’s what they are saying; big companies that deal in security vulnerabilities don’t quite agree. But first, let’s take a closer look at it.
Mimecast calls it ROPEMAKER, an acronym that stands for Remotely Originated Post-delivery Email Manipulation Attacks Keeping Email Risky, and it’s a means by which it’s possible to alter an email’s displayed content after it’s been delivered to the end-user’s inbox.
It uses everyday features that have been built into email systems over the years to make emails more interesting and attractive, like CSS and HTML.
The problem is that changing the display of the content of an email after it’s been delivered can defeat security measures that check emails before delivery. It also can lead the receiver astray and provides them with a false sense of security; after all, if the email is already in their inbox, it must be legitimate because IT’s already checked it, right? Wrong.
How it works
Let’s say an email arrives that’s formatted using CSS, a common internet technology that lets people make attractive emails. It looks great, all of the URLs it references are legitimate, and there’s no problem.
Except there is a problem – the html code in the email can reference CSS stored on a remote server, and should that remote server be under a cybercriminal’s control, any changes they make to it will be pushed through to the recipient’s email, changing what’s displayed. It’s what’s known as a “switch exploit”, as the attacker can switch legitimate info with malicious info at the click of a button.
So let’s say when the mail arrived, it referenced http://www.legitimateurl.com in a link in its body copy; an attacker could then change that link to, say, http://www.malware4lulz.com, post-delivery, and the end-user would be none the wiser. When it comes time to click the link, they will do so feeling confident they’ll be directed to the good URL.
How good is IT security, really?
Sure, this particular use of ROPEMAKER relies on the user’s browser successfully connecting to that dodgy site without their company’s web security software kicking up a fuss. But Mimecast isn’t convinced web security can catch absolutely everything that comes its way.
I spoke to Mimecast South Africa security expert, Brian Pinnock, who told me in a telephonic interview that there’s “not a lot of overlap” between security companies’ awareness of anti-virus signatures. What that means is that the big security software firms don’t always share everything they know with one another, leading to, at most, “a 20% overlap of knowledge between them” when it comes to virus signatures; thus, a malware signature that one is aware of is not necessarily automatically known to the rest. And when it comes to things like maintaining an up-to-date list of malicious URLs, the overlap between security vendors is not known at all, ”…mostly because it is such a moving target.”
But wait, there’s more
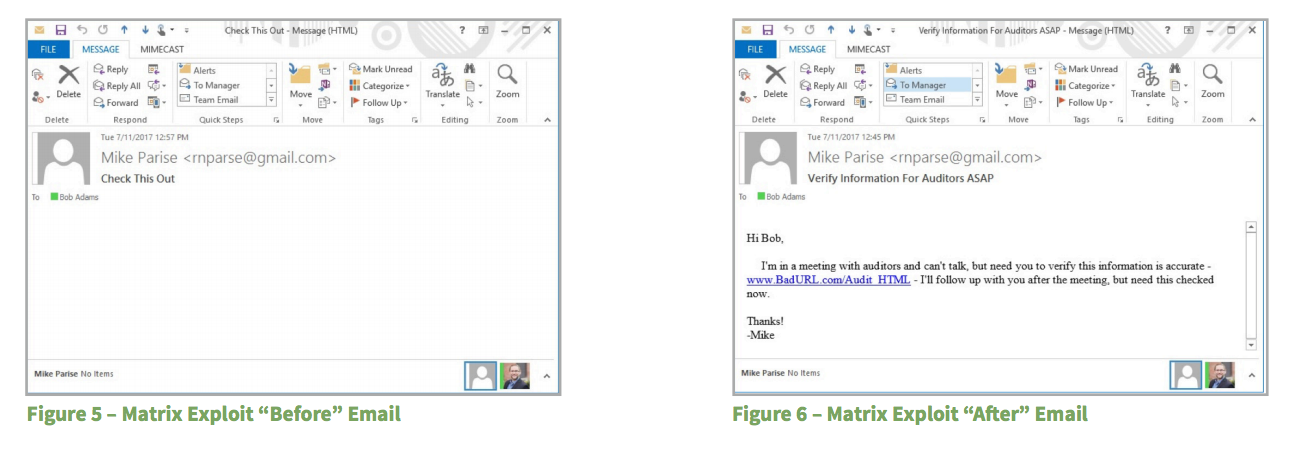
ROPEMAKER can also make use of another type of exploit that’s even harder to detect, called a “Matrix Exploit”.
This attack technique disguises itself by sending an email full of seemingly-random ASCII characters, the display of which are controlled by remote CSS; the initial mail can be disguised to appear completely empty and devoid of visible text or otherwise benign content, which is then remotely changed by the attacker into legible (and dangerous) text only after delivery.
The only giveaway of the emails’ possible intent is their large size and the volume of HTML tags in them – necessary for the “Matrix Exploit” to work.
I was told that ROPEMAKER only affects email clients like Outlook and Apple Mail, and not web-based email systems like Outlook.com and Google Mail. It can also be defeated entirely by not allowing emails delivered to those clients to reference outside resources; that disables it for all emails, though, which is less than ideal.
Mimecast, meanwhile, says that it’s able to protect its customers from ROPEMAKER-like exploits with a “Strip external source mode” command, an option found in the configuration of the Mimecast Targeted Threat Protection URL Protect service (part of the broader cloud-based email security gateway service provided by the company).
Nothing in the wild… yet
Mimecast stated in its initial blog post that they’d not yet encountered ROPEMAKER “in the wild”, meaning nobody had yet reported its use as part of a cyberattack. In addition, it’s proved difficult to define, falling somewhere between a vulnerability and a design flaw- depending on how you look at it, and who’s looking, it can be both… and neither.
This could have contributed to the fact that neither Microsoft nor Apple consider ROPEMAKER to be a threat. When Mimecast approached them about it, Microsoft politely (and a bit cheekily) referred Mimecast to a webpage that defines what a security vulnerability is, and Apple simply replied that ‘Users can choose to disable the loading of remote content by navigating to Mail > Preferences > Viewing and unchecking “Load remote content in messages”.’
While Mimecast has acknowledged to me directly via their Senior PR and Communications Manager, Richard Botley, that defeating ROPEMAKER can indeed be achieved by using certain mail clients or using a setting like with Apple Mail, he also said that doing so relies on an administrator knowing to set an extremely specific option to the correct setting, and breaking a lot of email formatting that many employees are now familiar with.
When I approached Microsoft myself, a spokesperson told me that “This case offers no serious security implications because by default, Outlook does not load external content from untrusted senders. We encourage customers to practice good computing habits online and to run up-to-date security software, such as Office 365 Advanced Threat Protection, and Windows Defender Advanced Threat Protection or Windows Defender.”
The problem
The problem is, according to Pinnock, that none of these solutions – even Mimecast’s – are a true “fix” to the issues raised by ROPEMAKER, as they don’t “…solve the problem for clients who might want to use remote CSS in a secure way.”
On getting these answers from Microsoft and Apple, Mimecast decided to take their findings about ROPEMAKER public. And this is where I came in – I was sent the report and asked to write about it by Mimecast’s PR people.
But as I wrote this story, it became apparent that something else has been going on, partly because Mimecast’s initial blog post stated they’d not encountered ROPEMAKER “in the wild” yet, and partly because of the tech industry’s responses to it. Why, then, would they be making noise about it?
It’s about web standards
So I asked them directly why they then went public with it, and was told “We believe that the industry as a whole needs to address this issue by changing standards amongst other things and making the issue public is simply a first step in that process.”
When pushed for clarification on what they believe “making the issue public” would achieve, I was told by Botley that yes, indeed, their aim was to create public pressure that they hoped would inspire the dialogue they believe is necessary to bring about the changes they’d like to see.
I then asked whether going public was the best move, as it would likely attract attention to ROPEMAKER, and potentially encourage hackers to use it in a future attack. Botley agreed that it was a possibility, but clarified that Mimecast believes the issues at stake are important enough for a proactive security disclosure. “Sitting on what we believe to be a dangerous attack without warning organisations about the risk they face today is not a risk worth taking”, he added.
Roots
So there you have it. ROPEMAKER is a real thing (although not yet a “threat”), big players in the security industry like Microsoft aren’t too worried about it, but Mimecast believes at its root are web standards that need overhauling for the modern era, and doing so is an imperative they believe the entire IT industry should be concerned with.
What are your thoughts? Is this a storm in a teacup, or should the industry be listening more closely to what Mimecast is saying?