Here’s a novel cybersecurity story that has us dumbfounded at how brilliantly simple it is.
Cybersecurity firm Intezer detected a ransomware operation that was targeting Linux-based file storage systems from QNAP.
The ransomware was dubbed QNAPCrypt and it functions just as you would expect ransomware to behave. It encrypts files and delivers a ransom note.
However, Intezer notes three key differences as regards QNAPCrypt:
- The ransom note was included solely as a text file, without any message on the screen—naturally, because it is a server and not an endpoint.
- Every victim is provided with a different, unique Bitcoin wallet—this could help the attackers avoid being traced.
- Once a victim is compromised, the malware requests a wallet address and a public RSA key from the command and control server (C&C) before file encryption.
Upon further investigation Intezer discovered that the Bitcoin wallets being used were static and created in advance. The ransomware would grab a wallet address from a list until all the wallet addresses had been used.
All of this means that Intezer could give the creators of QNAPCrypt a taste of their own medicine using a denial of service attack.
“After simulating the infection of more than 1,091 victims from 15 different campaigns, we encountered that the attackers ran out of unique Bitcoin wallets to supply to their victims,” the firm wrote in a blog post.
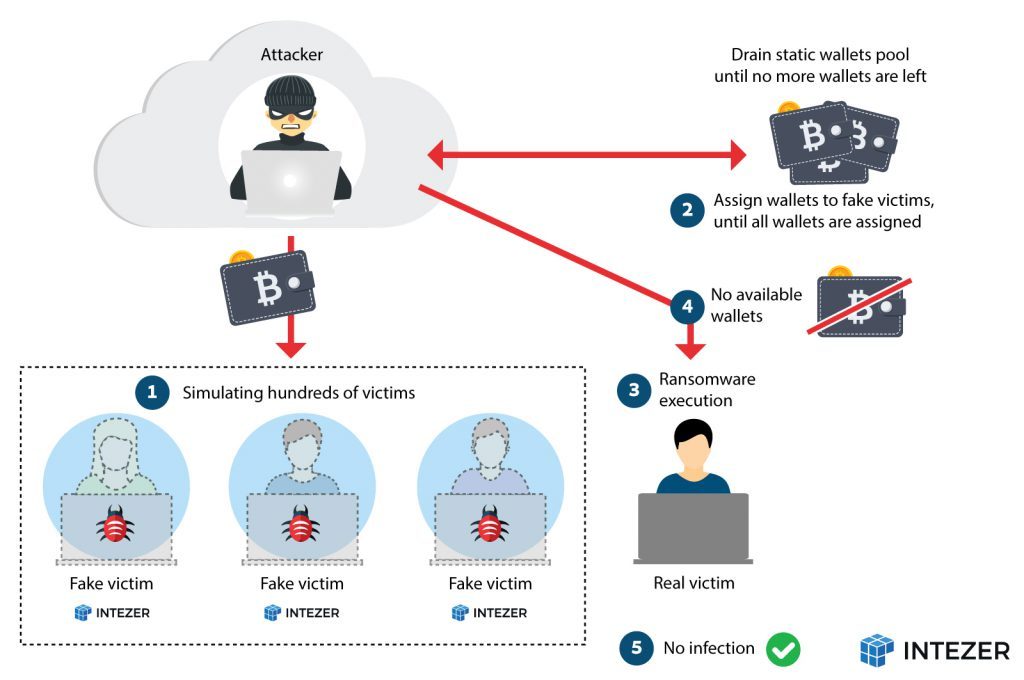 “As a result, any future infection will be unsuccessful and the authors behind this malware were forced to update their implants in order to circumvent this design flaw in their infrastructure to continue with their malicious operations.”
“As a result, any future infection will be unsuccessful and the authors behind this malware were forced to update their implants in order to circumvent this design flaw in their infrastructure to continue with their malicious operations.”
Unfortunately the creators of QNAPCrypt have updated the infrastructure to include the wallet and RSA key within the executable file that hits the target machine. This defeats the denial of service attack so crowning a winner is a bit tough from our side.
That having been said we find the fact that cybercriminals fell victim to a technique used by cybercriminals gave us a bit of a laugh.
You can read more about how Intezer fought this attack and discovered how to fight it over on its official blog.
[Image – CC 0 Pixabay]

